A vulnerability rated as High was recently patched in a Google Fonts optimization plugin for WordPress, allowing attackers to delete entire directories and upload malicious scripts.
OMGF | GDPR/DSGVO Compliant WordPress Plugin
The plugin, OMGF | GDPR/DSGVO Compliant, Faster Google Fonts. Easy., optimizes the use of Google Fonts to reduce page speed impact and is also GDPR compliant, making it valuable for users in the European Union looking to implement Google Fonts.
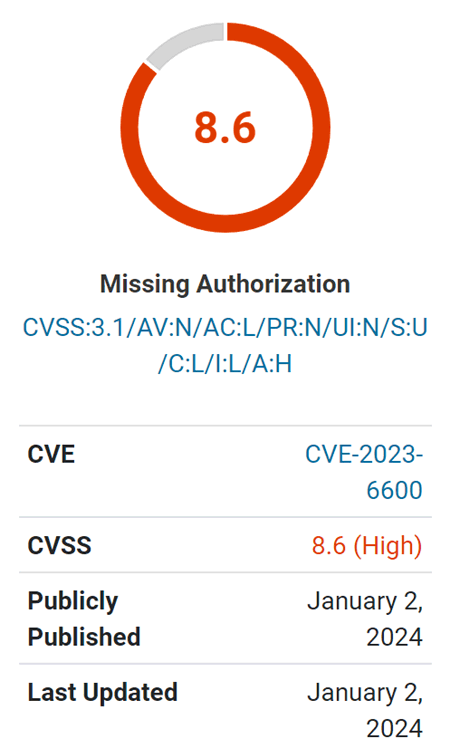
Screenshot of Wordfence Vulnerability Rating
Vulnerability
The vulnerability is particularly concerning because it allows unauthenticated attackers. “Unauthenticated” means that an attacker doesn’t need to be registered on the website or have any level of credentials.
The vulnerability is described as enabling unauthenticated directory deletion and allowing the upload of Cross-Site Scripting (XSS) payloads.
Cross-Site Scripting (XSS) is a type of attack where a malicious script is uploaded to a website server, which can then be used to remotely attack the browsers of any visitors. This can result in accessing a user’s cookies or session information, enabling the attacker to assume the privilege level of that user visiting the site.
The cause of the vulnerability, as identified by Wordfence researchers, is a lack of a capability check – a security feature that checks whether a user has access to a specific feature of a plugin, in this case, an admin-level feature.
An official WordPress developer page for plugin makers says this about capability checking:
“User capabilities are the specific permissions that you assign to each user or to a User role.
For example, Administrators have the “manage_options” capability which allows them to view, edit and save options for the website. Editors on the other hand lack this capability which will prevent them from interacting with options.
These capabilities are then checked at various points within the Admin. Depending on the capabilities assigned to a role; menus, functionality, and other aspects of the WordPress experience may be added or removed.
As you build a plugin, make sure to run your code only when the current user has the necessary capabilities.”
Wordfence describes the cause of the vulnerability:
“…is vulnerable to unauthorized modification of data and Stored Cross-Site Scripting due to a missing capability check on the update_settings() function hooked via admin_init in all versions up to, and including, 5.7.9.”
Wordfence also states that previous updates attempted to close the security gap but considers version 5.7.10 to be the most secure version of the plugin.
Read the Wordfence vulnerability warning:
Featured Image by Shutterstock/Nikulina Tatiana
